This article discusses about how to check for plagiarism. We often tend to have a lot of references to the work we do and sometimes even tend to use exactly the same references for our work.
Just to state an example, if a student in a university is assigned a project or research to work on, more than half of them end up going to Google in search of information. The action of stealing someone else’s work and claiming your rights on the same is how plagiarism is typically defined.
See Also: How to Publish an ebook?
Sometimes, we refer to some content online and change a few things to do what we are doing, which again leads to plagiarism. But, there is always an opportunity to improvise on the same, while building new content and ideas around and come up with something novel.
Plagiarism does not happen just in context to content; it also happens with technology as the intellectual properties and ideas, which they are based on, are always available on the public platforms. What most of the technologists do is refer to the ideas online and try and come up with something new.
This somehow is indirectly infringing the existing idea, but what matters is if your new idea is more of a utility to your use, is it developed, designed and presented differently.
A lot of people want to learn – how to check for plagiarism so that there is no infringement of copyrights issue and the originality of their efforts and work is retained. We will now take you through the basics of how you can check for plagiarism.
See Also: How to Use Microsoft Paint in Windows?
We will also throw some light on a few tools available online to do the same. We find most of these tools online available for free, which helps us make you understand what the differences between the free tools and the paid ones are and if it does make sense for you to use either a free tool or a paid one.
How To Check For Plagiarism Using Popular Tools
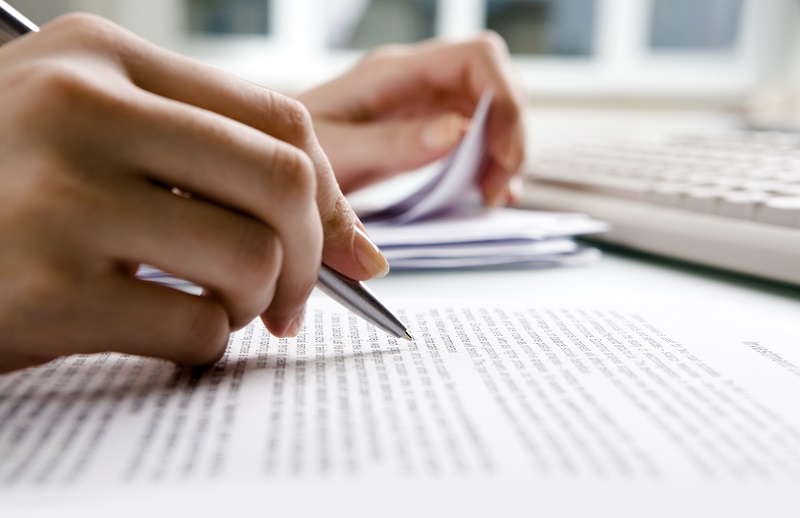
#1. Dupli Checker
Pros:
-
-
- You can check for plagiarism free with this tool.
- It is designed and developed to be simple, which makes it user-friendly.
- It comes with an option of copying and pasting the text. The user can even do a search using the URL to be checked or upload the file from the system.
- A registered account is allowed to do 50 checks per day.
- This is one of the most commonly and popularly used tools.
-
Cons:
- An unregistered account is allowed to do only 1 check per day.
Paid Version:
- There is no paid or premium version of this free plagiarism checker online tool.
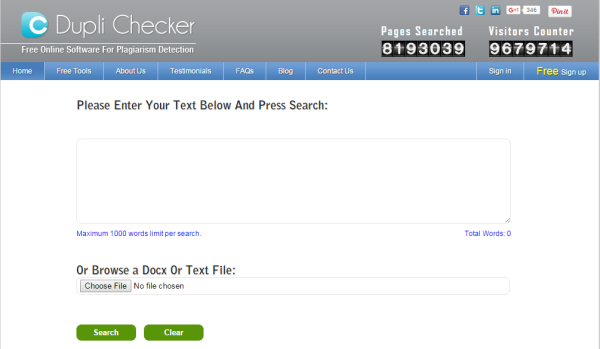
Copy Leaks
Pros:
- You can perform an entire website plagiarism scan using Copy Leaks.
- With a strong back end, this tool performs a check with about 60 trillion pages on the internet.
- It comes with inbuilt language packs and supports multiple languages.
- This tools also provides you with API with name Copy Leaks Service, which you could integrate with your system and automate it to do auto plagiarism search.
Cons:
- You can only do a check for online content such as websites.
- It’s essential for a user to have an account to use this tool.
Paid Version:
- The tool is currently free to use for anyone, but very soon Copy Leaks will have a paid model too.
Paper Rater

Pros:
- Comes with an offering of tools such as, plagiarism detection and writing suggestions.
- The development of this tool is done by a bunch of smart graduates.
- You can get Readability statistics using Paper Rater.
- It also provides you with title validation.
Cons:
- This tool does not allow you to save the reports of the scans you do.
Paid version:
- The paid version of Paper Rater allows you to put up to 6000 words.
- The processing speed, when compared to the other tool, is much faster.
- It’s an ad-free service.
- It comes with a document uploading ability.
- It is charged at about 8 dollars a month on an annual payment.
Plagiarisma
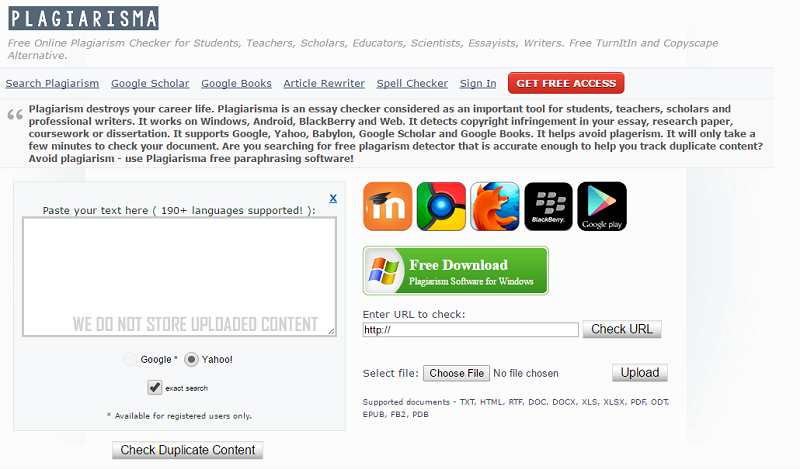
Pros:
- This tool is only available for Windows operating system and is a free tool currently.
- It supports close to 190 languages.
- It is easy to use and one of the preferred tools.
- The search for a website happens based on URL.
Cons:
- You get reports only for the exact matches.
- It comes with a Synonymizer tool, which in the result replaces the matching words with their synonyms.
- A registered user also can only do 3 scans or checks per day.
Paid version:
- The paid version of the tool comes with Unlimited plagiarism checker with which you can also schedule tasks.
- The basic model is charged at $5 per month.
Plagiarism Checker
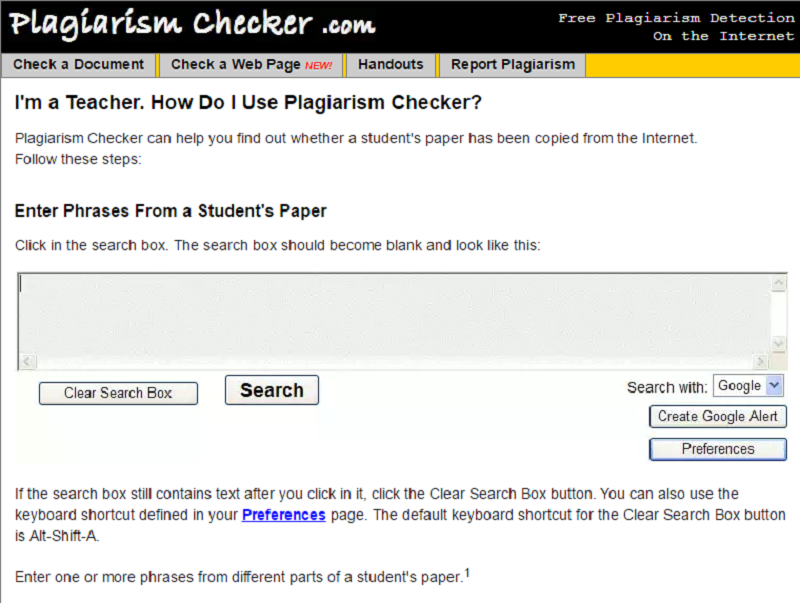
Pros:
- This is a free online plagiarism checker.
- The tool is designed well and is quite suggestive.
- Mostly suitable to use for the people from the education industry to perform checks on student assignments.
- The tool comes with an option “Author”, which helps you check if others have copied your work.
- It is a web-based application and does not need any download or installation.
Cons:
- Each phrase is separately checked, and you have to be adding extra efforts of hitting enter after every phrase.
Paid Version:
- There is no paid version of the tool currently available.
Plagium
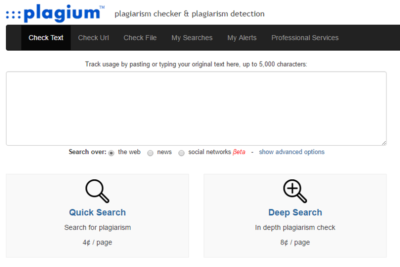
Pros:
- This tool works on the copy paste option and is very easy to use.
- It comes with an ability to scan up to 5000 words at a time.
- You can also use this tool to perform a search on the social media.
Cons:
- There are very few free tools. The payment here is based on your requirement of an extra feature.
Paid Version:
- Starts at a basic price of $4 and an extra payment based on what features you would want to go for
See Also: How to Take a Screenshot on Windows 10?
In this article, we have discussed the pros and cons of a few popular online tools to do the Plagiarism test. Hope that helps you understand which tool is best for your needs. You can now go ahead and explore these tools to check for Plagiarism.